Scams are becoming more dangerous and harder to spot. Here’s what to look for. Over the past few years, the public has grown more educated in the tactics used by online scammers. Doubtless, this is due to the rise in security breaches in prominent businesses and the surrounding publicity. With the news coverage surrounding these […]
Category Archives: Security
How to create checks and balances when organizing your IT network. When many people think about IT security, the first things that come to mind are programs such as firewalls or malware detection software. However, security is as much about the organization systems and process your company has in place as anything else. Of those […]
How to protect and control encryption key access across its lifecycle. Encryption technology is one of the most important security features protecting your data. The use of encryption-in-transit secures email, text, and web data so that users can send and receive information without fear of interception or tampering. Meanwhile, encryption at rest protects data where […]
Encryption at rest can protect your data, even if someone steals it. Data security comes in many forms. In order to keep your business safe from a security breach, you need to protect your data from destruction, spying, and outright theft. Protecting yourself requires different lines of defense, and at the forefront of these is […]
How can you protect your data as it moves from one location to the next? You’ve probably heard a lot about data encryption. It forms one of the pillars of IT security: without encryption, sensitive business information would be vulnerable to anyone who could steal or intercept it. However, data encryption uses complex algorithms to […]
How the Internet of Things adds an extra layer of risk assessment for businesses. Technology experts estimate that by Internet-enabled devices, soon to surpass smartphones, will number over thirty-billion objects by 2020. This Internet of Things (IoT), which includes objects such as thermostats, production sensors, and kitchen appliances, provides one of the top opportunities for […]
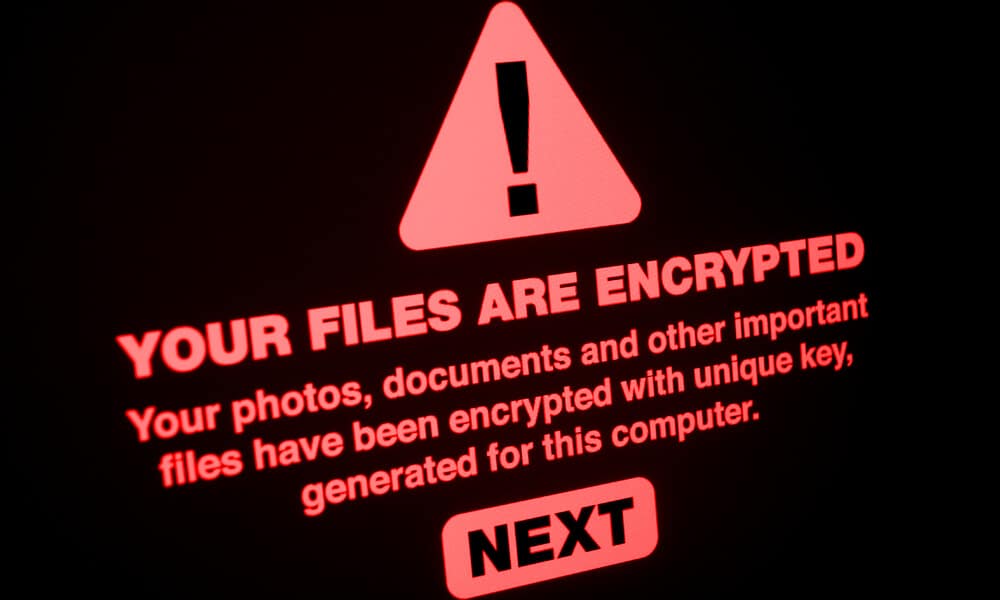
No cybersecurity defense is complete without breach detection and a response plan. We wrote last week about the threat ransomware poses to your business, and strategies you can use to prevent your system from being compromised. While ransomware can grind your business to a halt by holding your data hostage, there is one way in […]
Ransomware attacks are on the rise. Here’s how your business can detect and prevent them. 2017 has seen an increase in prominent ransomware attacks, and experts warn that they are likely to grow more common. So far, 2017 has seen two significant ransomware attacks: WannaCry, which began in May, and NotPetya, which followed a couple […]
How can you protect your data and IT resources in case of an emergency? Each year, companies invest billions of dollars into their IT systems. These include their networks, the hardware and software on which they run, and the processes they use to manage everything. Protecting this investment should be a top priority for your […]
What is a DDoS attack, and how can you protect your business? Distributed Denial of Service (DDoS) attacks are an increasingly common—and increasingly difficult to prevent—form of cybersecurity threat. When businesses first experience a DDOS attack, they frequently misdiagnose the situation as a down server or a failed application. This is because DDoS attacks target […]