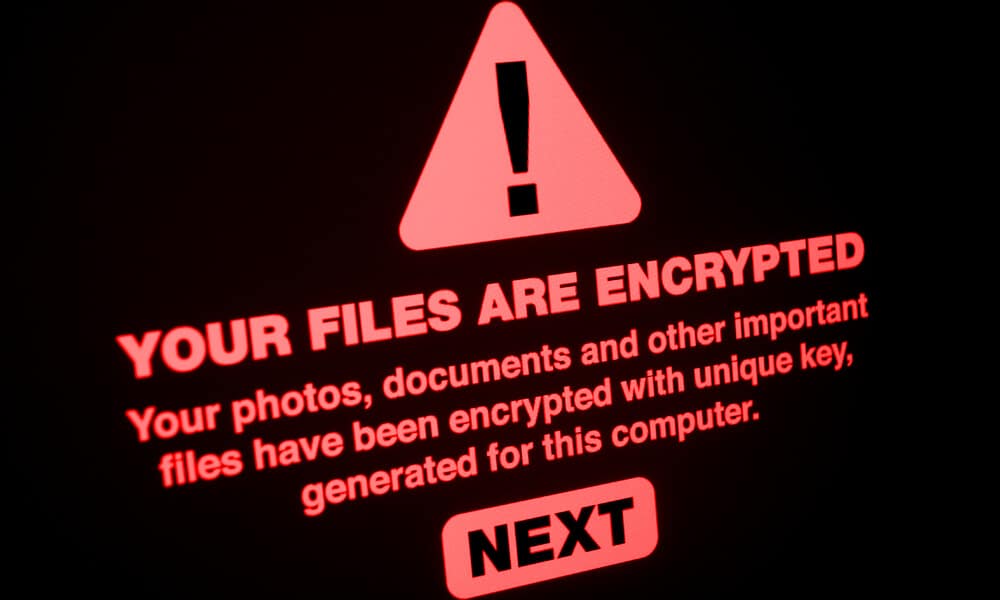
Ransomware attacks are on the rise. Here’s how your business can detect and prevent them.
2017 has seen an increase in prominent ransomware attacks, and experts warn that they are likely to grow more common. So far, 2017 has seen two significant ransomware attacks: WannaCry, which began in May, and NotPetya, which followed a couple weeks after. These cyberattacks drew international attention as they wreaked havoc across organizations around the world, and for good reason. However, one key lesson from these attacks was that they were entirely preventable.
Both WannaCry and NotPetya exploited a known weakness in Window’s Server Message Block protocol. Although Window’s had released a critical security patch two months previously, many users had not installed the update. Had these users done so, they would have been secure from attack—for this time, at least.
This is not to be overly harsh toward those businesses which fell victim to these viruses. The failure to keep systems updated is a common problem across many organizations, which is one reason it is so often used in malware attacks. However, it should inspire the rest of us to be more diligent in our IT security efforts. Here’s how you can keep your systems safe.
Disinfect, Decrypt, Defend.
If the worst happens and your system is hit with a ransomware attack, experts caution against paying for the decryption key. Their reasons boil down to two major concerns. First, ransomware attacks happen because they are successful ways of extorting money from those affected. Because of this, paying the ransom only encourages future ransomware attacks. Second, there is no guarantee you will get your data back, even if you pay the ransom. While some ransomware attacks return your data, many others don’t.
None of this means you are without recourse. If you have a recent backup, then you can work with your IT team to disinfect your system and restore your data from the backup. You will need to ensure that your system is entirely clean before restoring your data, otherwise you risk a recurring attack. Similarly, you will need to scan your backup to be sure it does not contain a version of the virus.
When a ransomware attack becomes widespread, researchers set to work cracking the virus to eliminate the threat. Because of this, there may be a published decryptor, depending on what ransomware you’re dealing with. This will only work if a decryptor has been created for the specific ransomware virus affecting your system.
Finally, there are several critical steps you can take to defend your system against future ransomware attacks. Many of these are IT security best practices which will guard against any number of other threats as well.
1. Stay up to date on security patches.
As we discussed at the beginning of this article, both WannaCry and NotPetya only affected systems that had not installed the most recent Windows security patch. While many of us treat security updates as an interruption and a nuisance, these attacks are a sobering reminder of how important security updates really are to the health of our IT systems.
That said, there are ways to manage your updates so that they do not interrupt workers during critical business hours. Our recommendation is to prioritize updates so that security patches happen immediately. Meanwhile, other system updates can be deferred till close of day and run at a set time, such as 3:00am, when users are unlikely to be working.
2. Maintain regular and secure backups.
Regular data backups are critical for businesses on many counts. After all, ransomware is only one of the risks your business faces for data loss. Data backups keep your business assets safe against power failure, system crashes, and lost or damaged equipment.
In the case of a ransomware attack, you will certainly be grateful to have a recent backup on hand. This is easily managed by working with your IT team to create a schedule so that the backups can happen automatically. You should also take precautions to ensure that your backups aren’t at risk for infection, either.
3. Create ransomware detection alerts.
Unlike most malware, which can lurk undetected within a system for months, ransomware works quickly and requires real-time monitoring to defeat. The good news is that there are several ways of detecting ransomware before it can damage your system.
First, many ransomware files use known file extensions, such as .crypt, .lock, and .enigma. A good anti-ransomware program can spot these files on your computer and quarantine them before they begin encryption of your data. However, this is not a foolproof system. The list of known ransomware file extensions is rapidly expanding, and there’s always a chance the extension will be something either incredibly common or never seen before.
Fortunately, ransomware detection programs can also spot suspicious activity and halt it before it goes too far. As an example, ransomware detection software can notice if many files are undergoing name changes within an exceptionally short period, and then flag the system administrator of a possible ransomware attack. For instance, files being renamed at a rate of more than four files per second is unusual activity even in a large network.
4. Limit access to sensitive data.
Firewalls are another important means of protection against malware and other viruses. A firewall can both block users from accessing certain websites, and it can block certain file downloads based on their type or their point of origin. You can also set up firewalls which isolate your most critical systems from other computers on your network. This can contain the spread of ransomware and limit its impact on your organization.
You should also set up systems which control user access to sensitive data. If fewer employees have access to critical data, it is less likely to be compromised. So, if one department needs broader access to the Internet, and therefore different firewall permissions, then you will also want to limit how those computers interact with the rest of your system.
5. Train your employees in safe computer usage.
Many viruses—not just ransomware—first enter a computer system through human error. By establishing security protocols and training employees in their proper use, you can help prevent an outbreak in your organization.
You can start by reminding employees not to click on suspicious links and showing them how to spot phishing scams in their inbox. But further training could include how to handle and store sensitive data, and what to do in case they spot suspicious activity. With ransomware, a fast response is the most critical factor in containing the threat.
Proactive security efforts offer the best protection.
Most ransomware threats do not target individual businesses. Instead, they look for the easy targets: known weaknesses in software programs, organizations with lax security standards, or overly gullible employees. These attacks are clever, and staying ahead requires expert knowledge and hyper vigilance. But failure is not inevitable. By creating and following strong security procedures, you can protect your organization against ransomware attacks.
Creating and integrating a strong security plan requires not only an in-depth knowledge of IT, but a robust understanding of the most recent threats. At Brightline IT, we pride ourselves on our high compliance standards and our in-depth knowledge of system security. If your business needs assistance in complying with industry security standards, or if you would like guidance on fortifying your current system, we offer a free security assessment. Contact us today.