The False Claims Act (FCA) was first passed during the Civil War, but it’s been used most commonly over the past 40 years. It allows citizens to report individuals or organizations who submit some sort of “false claim” and sue them for fraud on behalf of the government. Like many business owners, you probably find […]
Weekly reports, team meetings, slowed connection, blocked access, halting systems—an everyday work shift can quickly become a nightmare when you’re faced with a cybersecurity incident. It can be easy to panic in moments like these, especially if you’re not sure what you’re up against or the best way to respond. Taking a proactive approach is […]
In our hyper-connected world of technology, safeguarding your business from cyber threats is more critical than ever. At the heart of this defense is a robust cybersecurity framework. But what exactly does that mean, and why is choosing the right cybersecurity framework so vital for your business? What Is a Cybersecurity Framework? A cybersecurity framework […]
When you think of cybersecurity, encryption is probably one of the first things that comes to mind. For many businesses, ensuring the safety of sensitive data is an ongoing concern. But how does encryption work, and what exactly is it? In this blog, we’ll unravel the mysteries of encryption, and show you why it’s essential […]
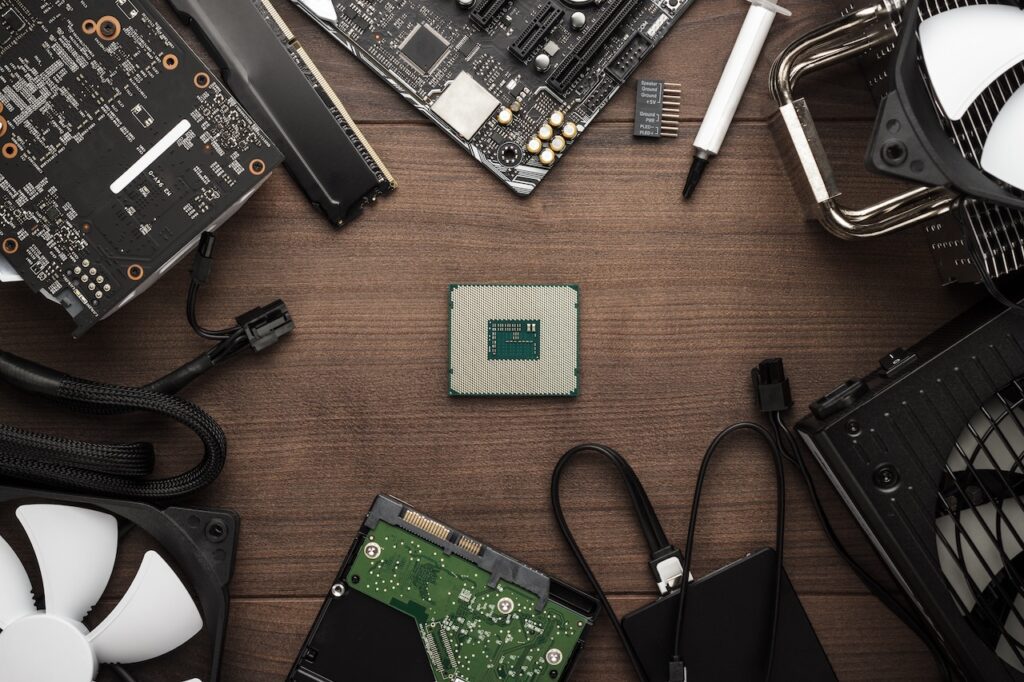
In today’s fast-paced technological world, working with old and outdated hardware can severely impact a company’s productivity, efficiency, and overall success. When faced with aging hardware, there are three main options before you: hardware maintenance, upgrades, or replacements. Each option has its own individual benefits and drawbacks, but ultimately the decision will depend on the […]
Introduced by the Department of Defense (DoD), CMMC aims to enhance the security of the Defense Industrial Base (DIB) by requiring contractors to implement stringent cybersecurity measures. Use this CMMC compliance checklist to make sure you’re on the right track and able to access all the benefits that come from being CMMC compliant. What Is […]
Cloud-based disaster recovery solutions are vital for modern businesses looking to safeguard critical data and operations. In the event of a natural disaster, cyber attack, or other unforeseen circumstances, having a reliable and efficient disaster recovery (DR) plan can mean the difference between business continuity and complete shutdown. But what exactly is cloud-based disaster recovery, […]
Phishing attacks are one of the most prevalent and damaging forms of cybercrime today. And the consequences for businesses and employees can be devastating—ranging from crippling data breaches and financial losses to severe damage to a company’s reputation. According to the FBI’s 2023 Internet Crime Report, phishing was the most common type of cybercrime, with […]
In the realm of healthcare, the sanctity of patient information cannot be overstated. As healthcare providers, insurers, and related entities rely on digital systems for processing medical records, maintaining compliance with the Health Insurance Portability and Accountability Act (HIPAA) has never been more critical. HIPAA security rules are not just bureaucratic hurdles; they are essential […]
Hackers used to target companies with large amounts of consumer data, but in recent years, they have shifted their focus to smaller companies, including those within the manufacturing industry. With valuable intellectual property and sensitive data being stored and transmitted throughout the supply chain, it’s no wonder manufacturers are a prime target for cyber attacks. […]